Endpoint Security , Governance & Risk Management , Patch Management
Windows Common Log File System Driver 0-Day Gets a Close-Up
Zscaler Researchers Probe File System Base Log File to Expose Flaw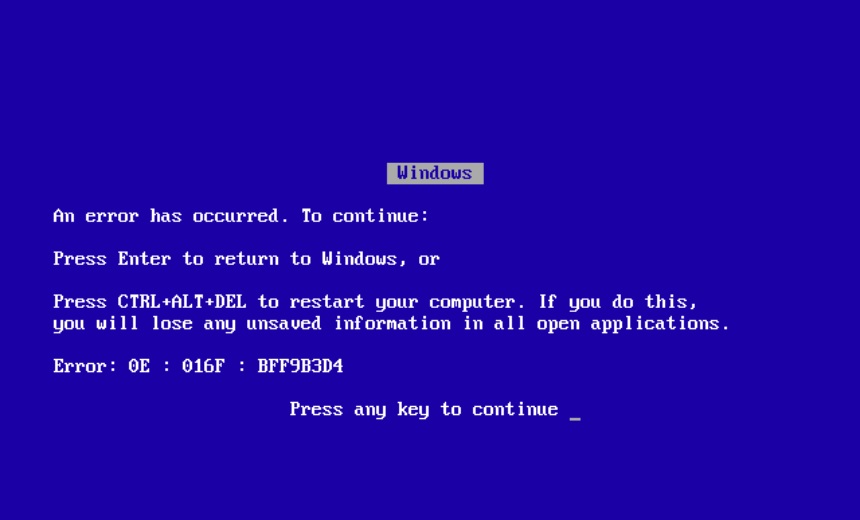
The function of a once-obscure subsystem in the Windows operating system called the Common Log File System is to record the transaction history of databases and messaging systems as an aid to functions including recovery support. The record is called a base log file.
See Also: Finding and Managing the Risk in your IT Estate: A Comprehensive Overview
Probe deep enough into the base log file and you might come out the other end with system-level access. The flaw, tracked as CVE-2022-37969, is not a secret: Microsoft patched it during September's monthly dump of security flaws (see: Microsoft Fixes Actively Exploited Zero-Day, 63 Other Bugs).
But even before Microsoft knew about it, somebody else did too, since the patch came with a warning that the vulnerability was being actively exploited in the wild. Its exploitation required an attacker to already have gained access to an endpoint. "Bugs of this nature are often wrapped into some form of social engineering attack, such as convincing someone to open a file or click a link," said Dustin Childs, a security analyst at Zero Day Initiative, at the time.
Now researchers on Zscaler’s ThreatLabz research team say they've identified the root cause of CVE-2022-37969.
In a nutshell, before the Common Log File System creates a log file consisting of the base log file, which consists of metadata blocks plus containers for storing actual data, each base log file begins with a header. In the header is the field cbSymbolZone. The field is normally unremarkable. In this context, it's important because when it's set to an invalid value, it can trigger an out of-bounds write.
To identify the root cause of the vulnerability, researchers developed a proof of concept triggering an operating system crash.
Exploiting cbSymbolZone to deliberately trigger Microsoft's dreaded blue screen of death - as opposed to, say, just letting Windows run until it triggers one itself - required Zscaler researchers to create a base log file with specific bytes in specific base log file metadata fields.
Through essentially a chain reaction created when attackers invoked the modified base log file, researchers triggered the system crash.
September's fix of a Common Log File System flaw was the first time Redmond found hackers using it for nefarious purposes. In an April 2022 blog post, cybersecurity firm PixiePoint Security said that the system first gained popularity as an attack vector in 2016, specifically as method of escaping browser sandboxes.