Sponsored by SailPoint
Sponsored by Elastic
As the SIEM Logs, So the SOC Responds: A Guide for Modern Security
Sponsored by Wiz
Frost Radar: Cloud-Native Application Protection Platforms, 2023
Sponsored by Palo Alto Networks
Meeting the Mandate: A Proactive Approach to Cybersecurity Compliance and Incident Reporting
Sponsored by Splunk & Optiv
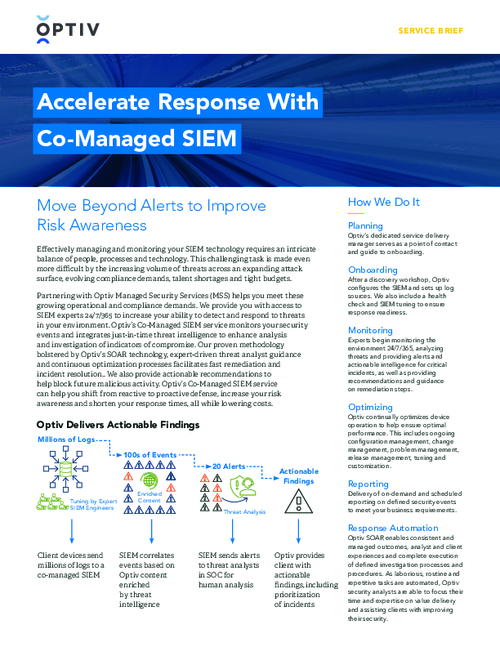
Accelerate Response With Co-Managed SIEM
Sponsored by Elastic
The Matrix of Security: Unplugged Insights and Virtual Realities
Sponsored by Wiz
CSPM Buyers Guide
Sponsored by Splunk x Optiv
eBook: Building Digital Resilience - How To Do It at Scale
Sponsored by Expel
Expel Quarterly Threat Report
Sponsored by VMware Carbon Black
Six Benefits of App Control Infographic
Sponsored by VMware Carbon Black
10 Things You Must Do to Secure Containers Now
Sponsored by Microsoft
eBook | Benefits of Automated XDR Platforms
Sponsored by Cloudflare
Cyber Security Best Practices For Financial Services
Sponsored by Cloudflare
Securing the Future: Asia Pacific Cybersecurity Readiness Survey
Sponsored by Mandiant