Sponsored by BitSight
Sponsored by BitSight
A Risk Manager's Guide to the GDPR
Sponsored by Alien Vault
GDPR Compliance Checklist: A 9-Step Guide
Sponsored by Alien Vault
Beginners Guide to SIEM
Sponsored by RiskRecon
Third-Party Cyber Risk: 8 Key Considerations
Sponsored by ThreatConnect
The Threat Intelligence Maturity Model: What You Need To Know
Sponsored by ThreatConnect
How Does The Evolving Threat Intelligence Platform Fit Into Your Cybersecurity Strategy?
Sponsored by CA Technologies
Combating Insider Threat and Targeted Breaches
Sponsored by CA Technologies
How can I counter the insider threats within my organization?
Sponsored by CA Technologies
Privileged User Governance - A Key to Effective Breach Protection
Sponsored by Fortinet
Data Security Under GDPR: How To Prepare For the Inevitable (French Language)
Sponsored by CA Technologies
The Total Economic Impact Of The CA Privileged Access Manager Solution
Sponsored by CA Technologies
A Privileged Access Management Maturity Model for Digital Transformation and Automation at Scale
Sponsored by CA Technologies
Using Threat Analytics to Protect Privileged Access and Prevent Breaches
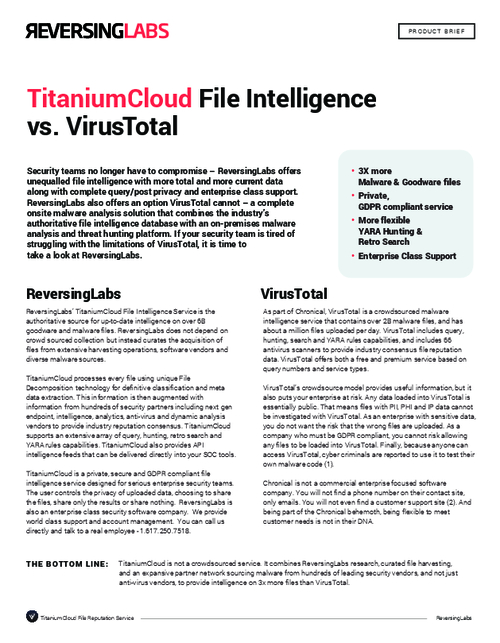
Sponsored by ReversingLabs