Sponsored by Sonatype
Sponsored by Palo Alto
Cloud Security Blind Spots: Detecting and Fixing Cloud Misconfigurations
Sponsored by Barracuda
The Evolution of Email Security
Sponsored by Ordr
EMA Zero Trust Networking Research Summary
Sponsored by Ordr
5 Ways to Improve Asset Inventory and Management Using Ordr
Sponsored by Gigamon
TLS Versions: North-South and East-West Web Traffic Analysis
Sponsored by ReversingLabs
How to Build an Effective Threat Intelligence Program
Sponsored by Cyberark
Making Cybersecurity a Business Differentiator for MSPs
Sponsored by IBM
Forrester Wave: Risk-Based Authentication, Q2 2020
Sponsored by IronNet
Dynamic Detection for Dynamic Threats
Sponsored by Secure Code Warrior
Why empowering developers to write secure code is the next wave of application security
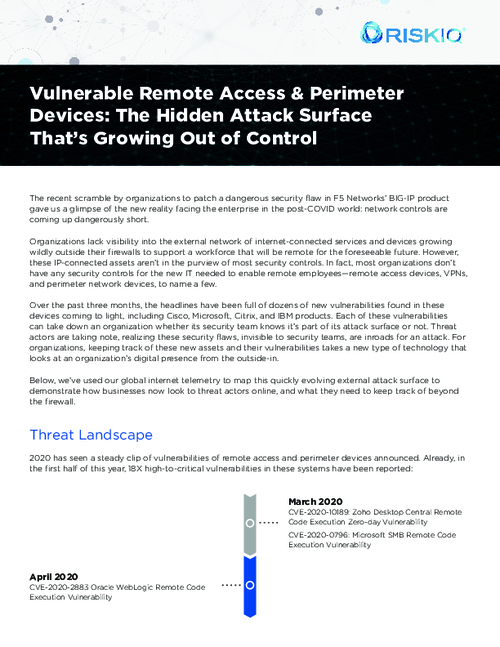
Sponsored by RiskIQ