The Effectiveness of BEC Attacks and Recent Examples
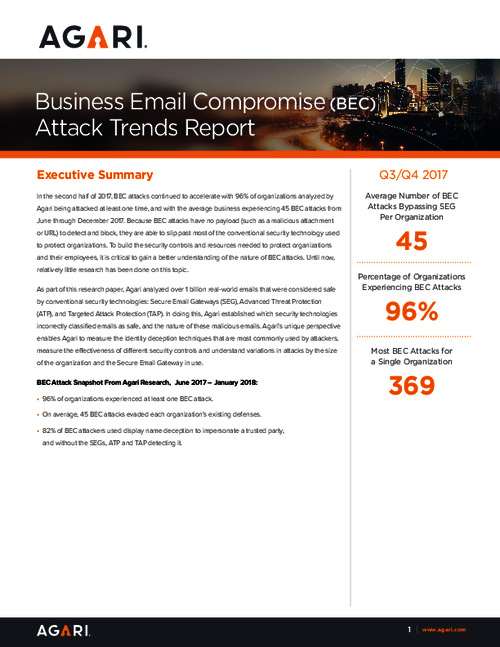
To build the security controls and resources needed to protect organizations and their employees, it is critical to gain a better understanding of the nature of BEC attacks.
Download this report based on exclusive BEC research and learn
- Statistics on BEC attacks by imposter type, SEG, company size & industry
- Which malicious emails bypass traditional email security protocols
- What a typical organization sending BEC attacks looks like and which processes they use to launch an attack.