Dutch and British Governments Slam Russia for Cyberattacks
Officials Attribute BadRabbit Ransomware, WADA Breach to APT28, aka 'Fancy Bear'
The British and Dutch governments have issued a strong rebuke to the Russian government over an ongoing series of hack attacks that they say were launched by the Russian Main Intelligence Directorate, aka the GRU.
The military intelligence agency has been tied to attacks that researchers have previously attributed to a group called APT28 or Fancy Bear.
The U.K.'s National Cyber Security Center, which is attached to the country's GCHQ intelligence agency, says the GRU's hacking operations are associated with - and known as - APT 28 and Fancy Bear. The group is also known as: BlackEnergy Actors, Cyber Berkut, CyberCaliphate, Pawnstorm, Sandworm, Sednit, Sofacy, Strontium, Tsar Team and Voodoo Bear.
U.K. Prime Minister Theresa May and Dutch Prime Minister Mark Rutte issued a joint statement on Thursday, timed to coincide with the U.S. Justice Department's indictment of seven GRU intelligence agents, based, in part, on intelligence provided by the Netherlands (see Feds Indict 7 Russians for Hacking and Disinformation).
"We have, with the operations exposed today, further shone a light on the unacceptable cyber activities of the Russian military intelligence service, the GRU," May and Rutte say in their joint statement. "It has targeted institutions across the world, including the Organization for the Prohibition of Chemical Weapons (OPCW) in The Hague."
Hackers seeking to undermine "an international organization working to rid the world of chemical weapons" is unacceptable, they said, but they say that attack is just one of many that have been attributed to the GRU.
"The GRU's reckless operations stretch from destructive cyber activity to the use of illegal nerve agents, as we saw in Salisbury [England]. That attack left four people fighting for their lives and one woman dead," they said.
"The cyber operation targeting the OPCW is unacceptable. Our exposure of this Russian operation is intended as an unambiguous message that the Russian Federation must refrain from such actions," says Dutch Defense Minister Ank Bijleveld. "The OPCW is a respected international institution representing 193 nations around the globe and was established to rid the world of chemical weapons. The Netherlands is responsible for protecting international organizations within its borders, and that is what we have done."
Fancy Bear Attacks
The U.K. government, based on intelligence gathered by GCHQ, says it assesses "with high confidence that the GRU was almost certainly responsible" for a number of attacks, including four that it is attributing for the first time:
- BadRabbit ransomware: October 2017 destructive malware campaign affected targets in Ukraine and Russia (see BadRabbit Attack Appeared To Be Months In Planning).
- WADA breach: In August 2017, hackers released athletes' confidential medical files, apparently stolen from the World Anti-Doping Agency, under the auspices of the "Fancy Bears' Hack Team" (see Hackers Dump US Olympic Athletes' Drug-Testing Results).
- DNC Hack: In 2016, multiple emails and documents stolen from Democratic National Committee officials were leaked online (see 10 Takeaways: Russian Election Interference Indictment).
- TV station: "Between July and August 2015 multiple email accounts belonging to a small U.K.-based TV station were accessed and content stolen," the U.K.'s National Cyber Security Center says.
NCSC previously attributed the June 2017 outbreak of NotPetya ransomware, which appeared to instead be merely a wiper, as well as the October 2017 VPNFilter malware attacks, to the GRU.
British officials believe that high-level Russian government officials ordered all of the above attacks, and they have slammed the Kremlin for the disruptive attacks.
"The GRU's actions are reckless and indiscriminate: They try to undermine and interfere in elections in other countries; they are even prepared to damage Russian companies and Russian citizens," said British Foreign Secretary Jeremy Hunt. "This pattern of behavior demonstrates their desire to operate without regard to international law or established norms and to do so with a feeling of impunity and without consequences."
NCSC has released a technical advisory on APT28 attacks, featuring indicators of compromise. It includes an analysis of tools commonly used by the GRU "to penetrate target networks," including X-Tunnel, X-Agent and CompuTrace.
Following today's exposure of past Russian cyber campaigns, we have published guidance to help mitigate against the tactics they use. This is technical advice for the network defender community https://t.co/d7oTom6jx5
— NCSC UK (@NCSC) October 4, 2018
Nerve Agent Attack
The public rebuke comes at a time of escalating tensions between Russia and Western Europe, compounded by a military-grade nerve agent attack in March against Sergei Skripal, 66, a former GRU agent, and his daughter Yulia Skripal, 33, who were living in Salisbury, England. While the Skripals survived, the attack also injured Detective Sergeant Nick Bailey, who responded to the incident, and later poisoned Charlie Rowley, who found a perfume bottle that appeared to have contained the nerve agent, and Dawn Sturgess, who sprayed on the substance and died.
Last month, the British government blamed Alexander Petrov and Ruslan Boshirov for the attacks, saying they are suspected GRU intelligence service officers. The men, both of whom appear to be in their early 40s, subsequently appeared in a Russian television interview, claiming that they had been vacationing in Salisbury. But CCTV footage released by the British government suggested the men had instead conducted reconnaissance of the Skripal resident. Their sequential passport numbers were reportedly also from a range of numbers reserved for Russian VIPs and members of the intelligence establishment, potentially operating abroad under cover.
British Prime Minister Theresa May said that based on intelligence gathering, her government had concluded that the attack was "not a rogue operation" but instead "almost certainly" by senior Russian government officials.
U.S. officials have charged the GRU with attempting to hack numerous organizations that were investigating or which had condemned Russia's state-sponsored doping program. Targeted organizations, according to the indictment, included the Canadian Centre for Ethics in Sports, the International Association of Athletics Federations, the Court of Arbitration for Sport, the Fédération Internationale de Football Association, or FIFA. Other organizations targeted by GRU, it says, included the organization for the Prohibition of Chemical Weapons in The Hague, as well as nuclear power research at Westinghouse Electric Corp. in Pennsylvania.

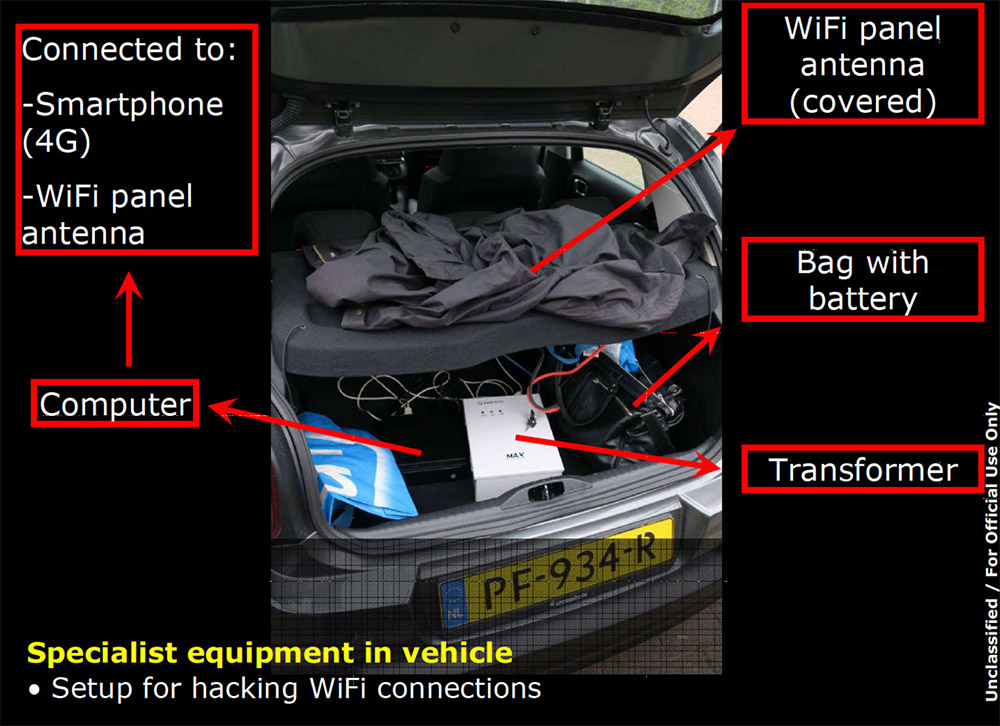
The Netherlands expelled four Russians in April after it caught them conducting reconnaissance of OPCW. Officials said the Russians' rental car contained contained specialized equipment designed to hack into computer networks or target individuals via their Wi-Fi connections, including hotel Wi-Fi.