Anti-Phishing, DMARC , Email Threat Protection , Endpoint Security
D-Link Routers In Brazil Fall To DNS Tampering
Remotely Exploitable Software Vulnerabilities To Blame For Hijacking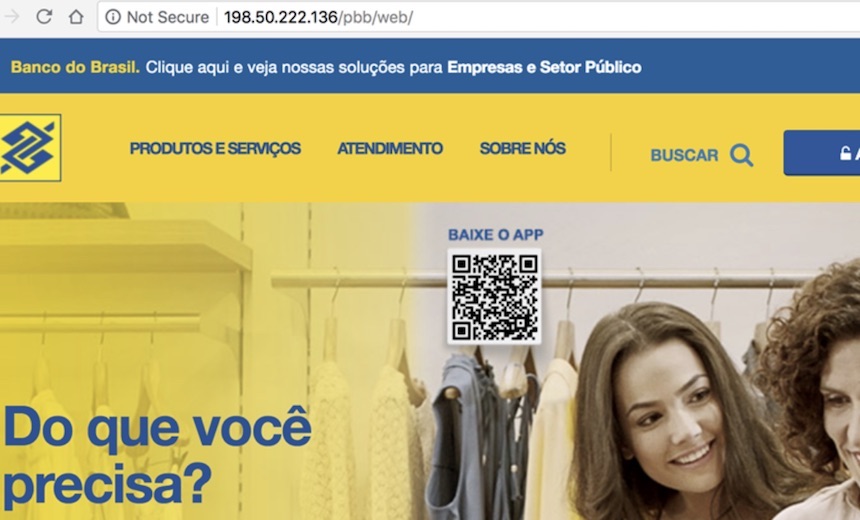
Cybercriminals in Brazil have capitalized on older vulnerabilities in D-Link routers for financially motivated phishing attacks.
See Also: Ransomware Costing Organizations Billions as CIO's and CISO's Lose Their Jobs
Analysts with Radware's Threat Research Center say they've noticed at least 500 attacks targeting D-Link DSL modems since June 8. Exploiting the vulnerabilities on the D-Link routers allowed the attackers to change the DNS settings on the victims' routers. The attacks originated with five servers in the U.S. and one in Brazil.
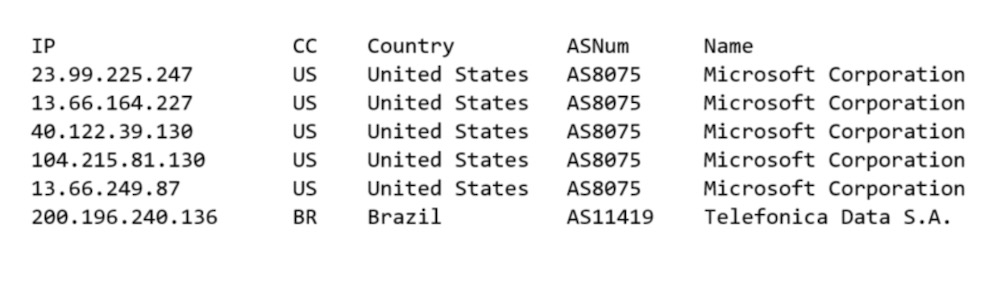
The attackers inputted the settings for their own malicious DNS server. When victims try to navigate to a legitimate banking website, they actually end up on a phishing site even though the URL appears to be same. Radware noticed one scheme that targeted Banco de Brasil.
"The malicious DNS server set up by the hackers becomes an effective man-in-the-middle that provides the malicious actor with the flexibility to bring up fake portals and web fronts to collect sensitive information from users whose routers were infected," writes Pascal Geenens, who is Radware's cyber evangelist in EMEA, in a blog post.
Router Meddling
Radware says it found several models of D-Link DSL routers with remotely exploitable vulnerabilities, including the DSL-2740R, DSL-2640B, DSL-2780B, DSL-2730B, and DSL-526B, as well as one from a different manufacturer, the Shuttle Tech ADSL Modem-Router 915 WM.
The malicious DNS server funnels most traffic to the correct websites as normal. But when a victim tried to navigate to Banco de Brazil, a phishing site would be served up instead, Geenens writes. The attackers also redirected requests for Unibanco, although no phishing site had been set up yet.
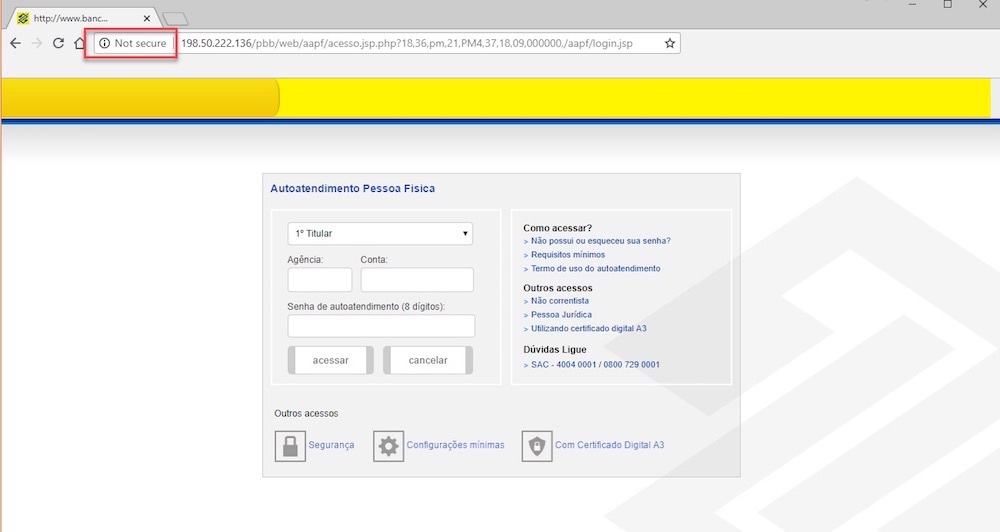
The fake Banco de Brasil site asked for information such as the bank agency number, account number and eight-digit PIN, Geenens writes. It also asks for a mobile phone number and payment card PIN.
Although the transfer to the phishing sites is seamless, Google's Chrome browser will display warnings that might help more astute users that something strange is afoot.
The bogus Banco de Brazil website has a self-signed TLS certificate, which will trigger a warning in Chrome. The bogus website will also be served up if people do not type "https" before the URL, but again, Chrome will display a warning that people should not go ahead.
Radware contacted both banks, Geenens writes. The Banco de Brasil phishing site is no longer active.
Aside from the phishing attempt, there's another risk for users. If the malicious DNS server goes offline, it's likely that those with infected routers won't be able to reach any services.
"The attacker is attempting to modify both primary and secondary name servers with the same malicious server IP, meaning that when the malicious server is offline, all infected homes will fail to further resolve any hostnames," Geenens writes. "Their internet will be virtually inaccessible until the users manually update their router settings or the ISP overrides the settings."
IoT Weaknesses
The broader issue is a well-known one: routers and other internet of things devices that are either hard to patch or are no longer serviced by manufacturers.
While awareness around IoT security issues has risen in recent years, it's a long-term problem. Manufacturers have been encouraged to engineer devices that are easy to patch for end users, but that's still far from a uniform practice (see Securing IoT Devices: The Challenges).
IoT devices such as home routers are rarely replaced unless there's a technical issue. It means devices could become increasingly more vulnerable as new problems are discovered.
With newer devices, there has been progress with issues such as default passwords. Several of the largest IoT attacks over the past few years were enabled by attackers finding devices with default passwords, making them easy to take over.
The Mirai botnet, for example, grew to as many as 300,000 devices in 2016. The malware used worm-like capabilities to spread by exploiting default and insecure passwords in routers, digital video recorders and IP cameras.
The Mirai botnet was then used for devastating denial-of-service attacks. In September 2016, its firepower was directed at DNS services provider Dyn, which resulted in disruption to services such as PayPal, Twitter and Spotify (see Can't Stop the Mirai Malware).